During scratch installation of Red Hat or CentOS, you can select the checkbox to encrypt all the available disks but it is also possible to encrypt root partition and other volumes once OS is installed. We will encrypt volume group and underlying physical volume and root partition with LUKS online using cryptsetup.
Below are some more articles on LUKS based Disk Encryption
- How to Encrypt Hard Disk (partition) using LUKS in Linux
- How to auto mount LUKS encrypted partition using fstab at boot in Linux
- How to encrypt root partition and entire file system using LUKS in Linux
- How to resize LUKS partition (shrink or extend encrypted luks volume) in Linux
- Configure LUKS Network Bound Disk Encryption with clevis & tang server to boot without password
Lab Environment
I have a Virtual machine with CentOS 8 Linux running on Oracle VirtualBox installed on my Linux Server. There are two disks attached to this VM.
First Disk → Size: 15GB → /dev/sda3 → The node is installed on
this disk which is un-encrypted.
Second Disk → Size: 20GB → /dev/sdb1 → We will use this disk to
move the all the available file system from /dev/sda3 which will be
encrypted with LUKS
These are the steps to replace an existing un-encrypted PV (/dev/sda3)
with an encrypted Physical Volume (/dev/sdb1) in a running/active
system for root volume:
Install Cryptsetup in Linux
To encrypt root partition and our physical
volume in Linux we need cryptsetup rpm
[root@centos-8 ~]# yum install cryptsetup -y
Encrypt alternate partition /dev/sdb1 with LUKS
Initialise new disk/partition as LUKS
device using luksFormat
/dev/sdb to create a new partition.
[root@centos-8 ~]# cryptsetup luksFormat /dev/sdb1
WARNING!
========
This will overwrite data on /dev/sdb1 irrevocably.
Are you sure? (Type uppercase yes): YES
Enter passphrase for /dev/sdb1:
Verify passphrase:
Open the encrypted LUKS device using a mapping. Here I am mapping my
LUKS device to /dev/mapper/secret. After this step you should see
/dev/mapper/secret encrypted file system on your LInux system
[root@centos-8 ~]# cryptsetup luksOpen /dev/sdb1 secret
Enter passphrase for /dev/sdb1:
Create Encrypted Physical Volume
Now we will start with the steps to encrypt root partition. The first
steps would be to create physical volume using our LUKS Mapping
/dev/mapper/secret.
[root@centos-8 ~]# pvcreate /dev/mapper/secret
Physical volume "/dev/mapper/secret" successfully created.
List the available physical devices. Currently as you see we have one
encrypted physical volume /dev/mapper/secret available on /dev/sdb1
and one un-encrypted physical volume /dev/sda3
[root@centos-8 ~]# pvs
PV VG Fmt Attr PSize PFree
/dev/mapper/secret lvm2 --- 19.99g 19.99g
/dev/sda2 rhel lvm2 a-- <14.50g 0
Encrypt Volume Group
Next extend the volume group by adding the newly created physical volume. With this we are one step closer to encrypt volume group in our Linux system.
[root@centos-8 ~]# vgextend rhel /dev/mapper/secret
Volume group "rhel" successfully extended
List the available Volume Groups. As you see our VG has two physical
volumes wherein one of the PV /dev/mapper/secret is LUKS encrypted.
[root@centos-8 ~]# vgs
VG #PV #LV #SN Attr VSize VFree
rhel 2 2 0 wz--n- 34.48g <19.99g
List the available Physical Volumes. As you see in the encrypted
Physical Volume we have 19GB free while un-encrypted PV (/dev/sda3)
has content of 14.5GB so we can easily migrate the content to encrypted
physical volume.
[root@centos-8 ~]# pvs
PV VG Fmt Attr PSize PFree
/dev/mapper/secret rhel lvm2 a-- <19.99g <19.99g
/dev/sda2 rhel lvm2 a-- <14.50g 0
Encrypt root partition with LUKS
Our root and swap partition are logical volume in rhel volume
group. Now since we have added encrypted physical volume to our existing
volume group. We will move the content of PV1 (/dev/sda3) to PV2
(/dev/mapper/secret) using pvmove
[root@centos-8 ~]# pvmove /dev/sda2 /dev/mapper/secret
/dev/sda2: Moved: 0.05%
/dev/sda2: Moved: 6.44%
/dev/sda2: Moved: 32.93%
/dev/sda2: Moved: 58.18%
/dev/sda2: Moved: 78.15%
/dev/sda2: Moved: 100.00%
As you see now our encrypted physical volume has all the content from
PV1 /dev/sda3 and PV1 is empty.
[root@centos-8 ~]# pvs
PV VG Fmt Attr PSize PFree
/dev/mapper/secret rhel lvm2 a-- <19.99g 5.49g
/dev/sda2 rhel lvm2 a-- <14.50g <14.50g
Similar using vgs we see our VG have 2 physical volumes
[root@centos-8 ~]# vgs
VG #PV #LV #SN Attr VSize VFree
rhel 2 2 0 wz--n- 34.48g <19.99g
To encrypt volume group, since we have migrated our data to encrypted
physical volume, we can remove the un-encrypted physical volume from the
rhel VG.
[root@centos-8 ~]# vgreduce rhel /dev/sda2
Removed "/dev/sda2" from volume group "rhel"
Once done also remove the un-encrypted physical volume to completely encrypt volume group as we do not have any more un-encrypted physical volume.
[root@centos-8 ~]# pvremove /dev/sda2
Labels on physical volume "/dev/sda2" successfully wiped.
Update encrypted LUKS device details in GRUB2 and /etc/crypttab
Now since we have migrated all the data to encrypted LUKS device to
encrypt root partition, we must also configure our GRUB2 to handle the
reboot. Update LUKS device details in /etc/crypttab and grub.cfg
We will update /etc/crypttab with the key details of our LUKS
device.
This command will generate UUID of our LUKS device and append the same
to /etc/crypttab
[root@centos-8 ~]# echo "luks-$(cryptsetup luksUUID /dev/sdb1) UUID=$(cryptsetup luksUUID /dev/sdb1) none" >> /etc/crypttab
/etc/crypttab
[root@centos-8 ~]# echo "luks-$(cryptsetup luksUUID /dev/sdb1)"
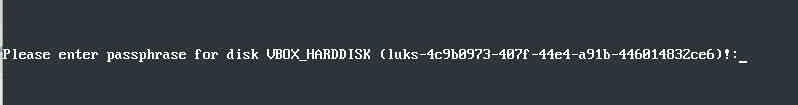
luks-4c9b0973-407f-44e4-a91b-446014832ce6
Below is my crypttab file content
[root@centos-8 ~]# cat /etc/crypttab
luks-4c9b0973-407f-44e4-a91b-446014832ce6 UUID=4c9b0973-407f-44e4-a91b-446014832ce6 none
Next update /etc/sysconfig/grub by adding rd.luks.uuid=<UUID> of the
LUKS device as
highlighted. This UUID should be the same as we added in
/etc/crypttab
[root@centos-8 ~]# cat /etc/sysconfig/grub
GRUB_TIMEOUT=5
GRUB_DISTRIBUTOR="$(sed 's, release .*$,,g' /etc/system-release)"
GRUB_DEFAULT=saved
GRUB_DISABLE_SUBMENU=true
GRUB_TERMINAL_OUTPUT="console"
GRUB_CMDLINE_LINUX="crashkernel=auto resume=/dev/mapper/rhel-swap rd.lvm.lv=rhel/root rd.lvm.lv=rhel/swap rhgb quiet biosdevname=0 net.ifnames=0 rd.luks.uuid=4c9b0973-407f-44e4-a91b-446014832ce6"
GRUB_DISABLE_RECOVERY="true"
GRUB_ENABLE_BLSCFG=true
rd.lvm.lv=/ and again
rd.lvm.lv=/
Next rebuild your GRUB2 configuration using grub2-mkconfig
[root@centos-8 ~]# grub2-mkconfig -o /etc/grub2.cfg
Generating grub configuration file ...
done
Rebuild initramfs:
[root@centos-8 ~]# dracut -f
Now you can reboot your Linux node. Since we encrypt root partition the boot up screen will prompt you for the LUKS passphrase before coming UP.
In our next article I will explain all about Network Based Disc Encryption (NBDE) wherein you can configure a tang server to get the key so that the system with encrypt root partition will automatically fetch the key from the tang server and continue to boot.
Lastly I hope the steps from the article to encrypt root partition, encrypt volume group and have an encrypted physical volume using LUKS in Linux was helpful. So, let me know your suggestions and feedback using the comment section.
References:
pvmove man page
vgreduce man page


